Debug and Trace Support for NXP S32N55 Vehicle Processor

Lauterbach’s TRACE32® development tools now support NXP® Semiconductors’ S32N55 vehicle super-integration processor for consolidation of real-time vehicle functions in software-defined vehicle (SDV) architectures. TRACE32® tools support includes simultaneous debugging of the processor cores as well as non-intrusive processor trace capture.
The S32N55 real-time super-integration processor combines high-performance real-time processing, a firewalled hardware security engine, and hardware isolation and virtualization for safe and secure integration of real-time vehicle functions. The SoC implements 16 split-lock Arm® Cortex®-R52 cores operating at up to 1.2 GHz, as well as two Arm® Cortex-M7 in lockstep configurations serving as system manager and communication manager.
Lauterbach’s TRACE32® development tools enable hardware-accelerated debugging and real-time tracing of all the Arm® processors and other cores that are implemented on the chip. TRACE32® tools consist of the universal PowerView debugging and tracing software as well as debug and trace accelerator modules. While Lauterbach’s intelligent PowerDebug modules provide the highest available download speeds and smallest response times for efficient debugging and test automation, PowerTrace real-time trace modules provide full insights of what the processors and other cores of the system are doing without impacting its real-time performance in any way. Trace analysis including code coverage measurements can support bringing embedded designs to market faster, safer, and more reliably than ever.
TRACE32® enables simultaneous debugging and tracing of the Arm® processors and other cores in a SoC; a unique capability to cover the whole system, regardless of whether the system is SMP (Symmetric Multiprocessing), AMP (Asymmetric Multiprocessing), or iAMP (Integrated Asymmetrical Multiprocessing). Lauterbach’s innovative iAMP debug and trace technology enables to debug multicore systems with identical CPU instruction sets in just one TRACE32® PowerView GUI.
“NXPs real-time super-integration processor S32N55 for software-defined vehicle architectures provides excellent computing performance as well as interfacing and functional safety features”, says Norbert Weiss, Managing Director at Lauterbach GmbH. “With the latest support of TRACE32®, we enable S32N55 customers to develop their applications with our market leading debug and trace tools right from the start.”
“NXP’s S32N55 processor is pioneering the super-integration of vehicle functions in central compute applications, enabling automakers to achieve significant cost and development efficiencies,” said Brian Carlson, Global Marketing Director for Automotive Processors at NXP. “Lauterbach’s TRACE32® development tools’ powerful debugging capabilities and insights offer complementary value, enabling developers to maximize their software performance.”
Lauterbach’s TRACE32® development tools enables developers of automotive SDV architectures to evolve their applications based on S32N55 SoCs even faster and easier.
About LAUTERBACH
Lauterbach is the leading manufacturer of cutting-edge development tools for embedded systems with more than 45 years of experience. It is an international, well-established company, serving customers all over the world, partnering with all semiconductor manufacturers and growing steadily.




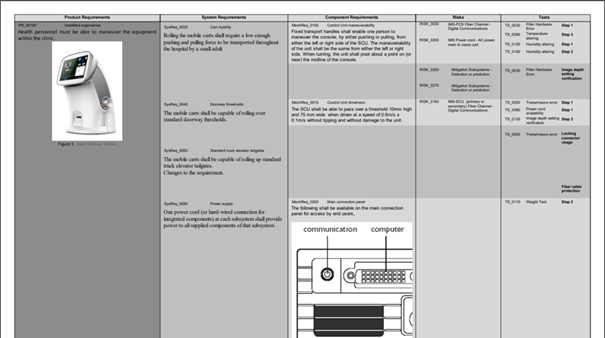 A well-designed traceability associates each requirement with the appropriate business objectives, making the evaluation of potential changes quick and easy, reduces project risk, promotes consistency between requirements, allows monitoring and control across the lifecycle of requirements, and more.
A well-designed traceability associates each requirement with the appropriate business objectives, making the evaluation of potential changes quick and easy, reduces project risk, promotes consistency between requirements, allows monitoring and control across the lifecycle of requirements, and more.
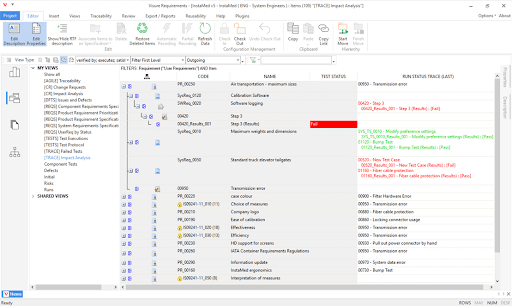 The problem is that manually describing and tracking the life of a requirement from its conception, through the specification and development, and down to its deployment is nearly impossible on complex projects with thousands of artifacts. Requirements management tools such as
The problem is that manually describing and tracking the life of a requirement from its conception, through the specification and development, and down to its deployment is nearly impossible on complex projects with thousands of artifacts. Requirements management tools such as 